Outsourcing accelerates your business into top gear
Free your business of accounting, HR and administration headaches by outsourcing these functions. You can focus on your clients with the utmost confidence that all your statutory obligations are being fulfilled.
The solution you are looking for is F2O. We have been providing peace of mind to our clients for over 25 years.
Call or email us now for a free consultation. We guarantee you won’t regret it.
Services to streamline your business.
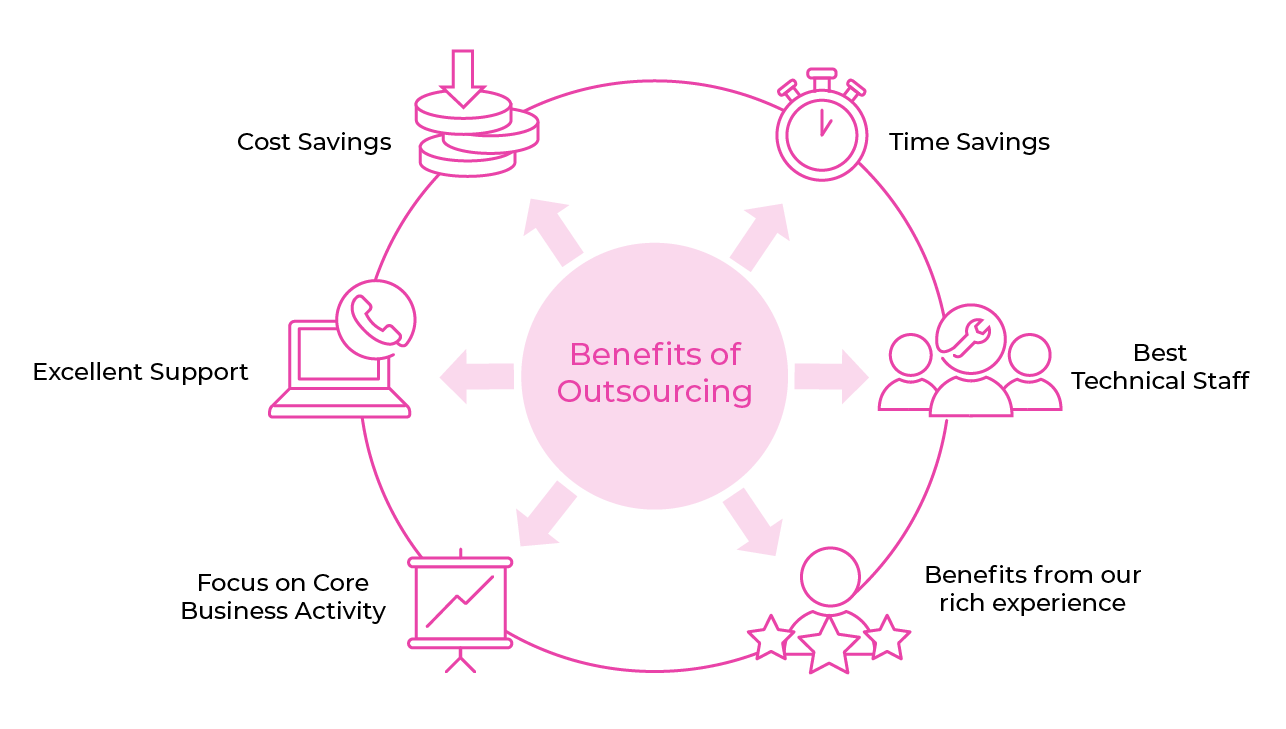
Advantages of Outsourcing
There are many benefits to outsourcing including reducing costs and ensuring back-office functions are looked after by individuals who are up to date with the latest legal requirements and industry practices. Having trained professionals completing the work increases efficiencies and profitability.
New businesses can follow ”a lean start-up model” to keep costs down, improve the business model and spend money where required, outsourcing removes the requirement to scaling up in-house resources.
Outsourcing provides a breadth of skill base and expertise not generally available in a single hire.
- Frees up resources - you or members of your team can outsource various tasks to F2O
- Improves processes and workflow - best practice is used from experience
- Provides off site security - for sensitive data
- Specialised knowledge and reduced training costs - all our employees are fully trained
- Cost effective - you only pay for services you use and can fix your fees
- Lower cost - fixed fees and less employees required
- Improved technology - your company would not need the level of IT and telephony we have
- Continuous support - no interruptions caused by holidays, sickness etc
- Healthier work/life balance - free up more of your time
“There are two good things in life - freedom of thought and freedom of action.”
W. Somerset Maugham (1874-1965), British novelist and playwright.